WaTech's Office of Cybersecurity is seeing a new phishing campaign that tries to trick people into revealing their work login credentials. The twist to this campaign is that it also tries to trick users into authorizing a two-factor authentication request that allows bad actors access to their accounts.
Here's an example of what we're seeing:
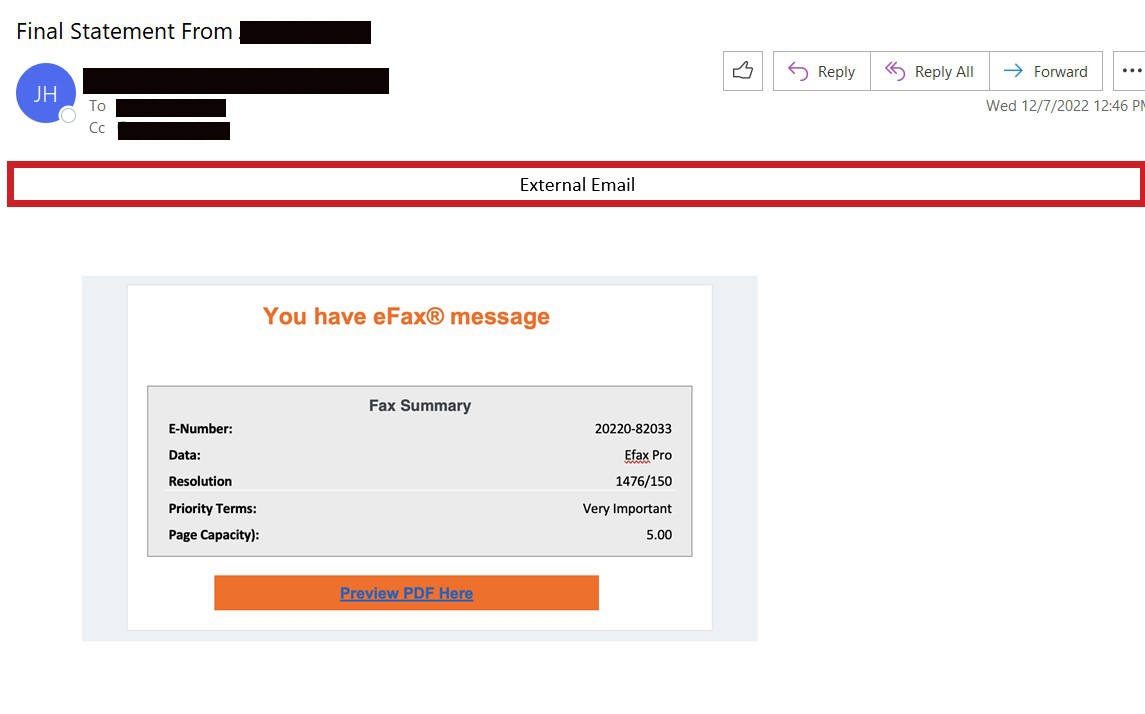
1. A phishing email says you have an eFax message.
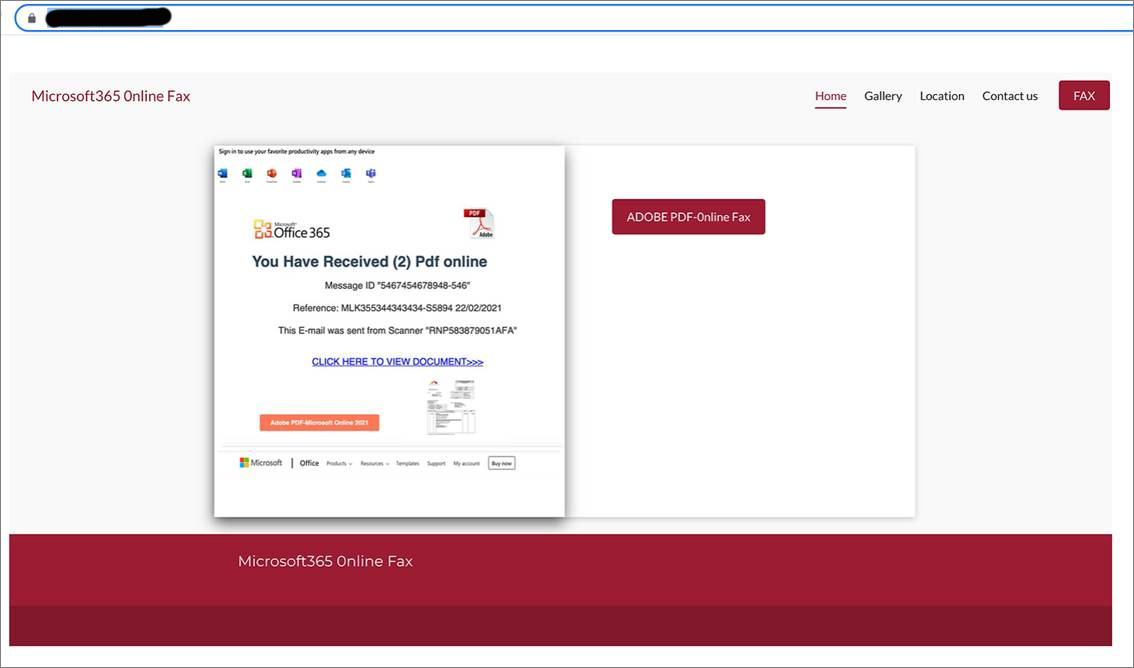
2. User clicks on a link that takes them to a new page listing the supposed documents.
3. If the user clicks on the link to access documents and it will take them to a page to login or verify identity.
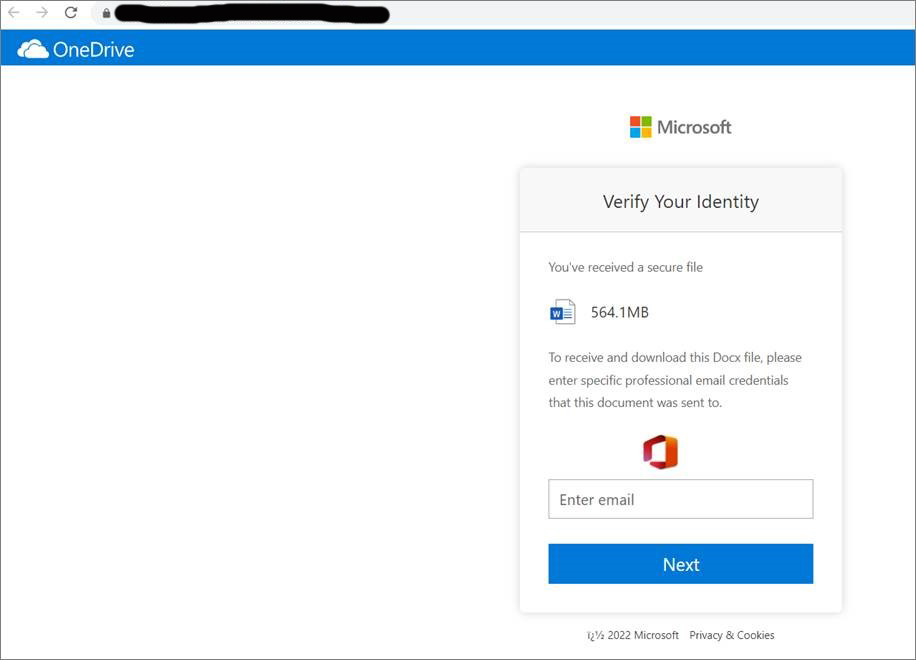
4. If a user provides the credentials, the bad actor attempts to login with the credentials provided. The user will get an MFA prompt to either Allow or Deny access.
Phishing tips
The most common way computer systems become infected with malware is through phishing emails.
It only takes one person to open an infected attachment, click on a link that goes to a malicious website, or be tricked into providing their account credentials.
Phishing emails are increasingly sophisticated and hard to detect. They may appear to be from people or organizations you know and trust. They may even contain information from previous emails threads so that it appears to be part of a continuing conversation.
General tips to avoid becoming a victim:
- Be suspicious of any emails that urge you to take action and try to create a sense of urgency.
- Never click on links or open attachments without first making sure the request is authentic.
- Call the sender by looking up their phone number independently.
- Never call a phone number included in a suspicious email, or reply to the sender.
- You can also hover your mouse over links to determine the full address.
Common types of attachments seen in phishing campaigns:
- Malicious files with innocent names, such as "invoice."
- Compressed or .zip/.rar files that can fool your anti-virus if it cannot inspect the files.
- Office products such as Excel and Word can have malicious macros (programs that run inside of programs).
- PDF files may have a malicious link or a macro embedded.
- Files that emulate a DVD drive or a USB drive (extension .iso, .ism) can be used to automatically run a script once opened.
Common ways bad actors try to trick you:
- New cat video. Can you believe this?
- Your organization just received an award, or you were recognized in a staff meeting.
- A popular band is coming to town, are you going?
- You have an imminent deadline for sexual harassment training.
- Sense of Urgency: Your password is about to expire, a deadline is approaching for mandatory training, overdue bill, we have not received your payment, a delivery attempt was made, your mail is on hold, your account credentials have been compromised, there is a warrant out for your arrest.
If you are a state employee and receive a suspicious email at work, please contact your information technology (IT) security staff immediately.
